Two weeks ago I was fortunate enough to attend Cisco Live (previously networkers).
Part of my goal there was to get clued up on IPv6 transition methods, addressing and all related matter. One of the breakout sessions I attended was on IPv6 security threats and mitigation. All in all very informative, but the major advice for networks not currently running IPv6 was to monitor your IPv6 flows to see what applications and operating systems were doing. Technologies like ISATAP are bound to break security boundaries by tunneling via IPv4 and this is something you should be aware of on your network.
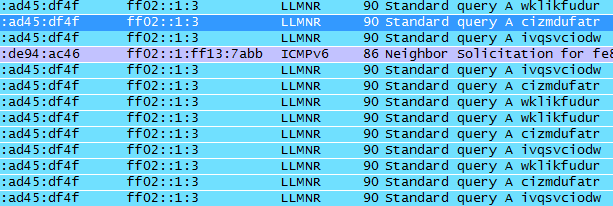
Today I started this quest just by running a regular wireshark session filtering via IPv6. Without a tap or a port span I could only observe multicast traffic, but I picked up on the below packets.
My immediate thought was a users PC was infected with a virus that was acting as part of a botnet and that this PC was using IPv6 to perform its DNS lookups. I went searching for 10 character IPv6 DNS lookups. Luckily what I found meant it wasn’t part of a botnet but I definitely wasn’t expecting what I found. This case has been documented before, so this is definitely nothing new and the fact that this happens in both IPv4 and IPv6 isn’t a suprise. Here are the references I found:
http://code.google.com/p/chromium/issues/detail?id=47262
http://groups.google.com/a/chromium.org/group/chromium-discuss/browse_thread/thread/17bd3e93f3c68448?pli=1
https://isc.sans.edu/diary.html?storyid=10312
http://groups.google.com/a/googleproductforums.com/forum/#!category-topic/chrome/report-a-problem-and-get-troubleshooting-help/dQ92XhrDjfk
As the reports suggest it’s a feature of Chrome to perform fake DNS lookups to determine if your ISP is performing DNS hijacking. In my case our DNS suffix provided by our DHCP server did not get appended, nor was the request a truncation of a proper URL nor was it over IPv4 – but it is most definitely the cause of the events I saw on the network.
As the quest for IPv6 and related security problems goes on I’m sure to throw more stuff up here.
Just scrolling through /. and noticed this article:
“Michael Geist reports that last week State of Maryland prosecutors were able to obtain a warrant ordering Verisign, the company that manages the dot-com domain name registry, to redirect the website to a warning page advising that it has been seized by the U.S. Department of Homeland Security. The message from the case is clear: all dot-com, dot-net, and dot-org domain names are subject to U.S. jurisdiction regardless of where they operate or where they were registered. This grants the U.S. a form of ‘super-jurisdiction’ over Internet activities, since most other countries are limited to jurisdiction with a real and substantial connection.”
I’ve been fearful of this for a while and watching this develop over the last year or so. I’ve never understood the legailities involved with the US seizing a site with it’s information when it’s clearly hosted in another country. I guess the loophole has been the ownership of the .com registrar, allowing a pivot for governments to obtain the remainder of the information past the actual domain name. A loophole which is now firmly stated.
I guess the only hope now is one that comes from more awareness. If you don’t want to have your domain seized due to the content on your site – don’t register it through a .com .net or .org.
Recently I purchased the Blackberry Storm which is exclusive to Vodafone here in Australia.
I have had some problems finding the initialisation commands for Vodafone in Australia.
Here is the process.
Installing the Blackberry Storm will install 3 modems:
– Standard 33600 bps Modem
– Standard 33600 bps Modem #2
– Standard Modem
Leave the first two alone, but under the standard modem in the advanced properties, enter:
+cgdcont=,,"vfinternet.au"
Next create a new manual internet connection and when it asks for a password enter *99# and do not enter any username or password
Open up the Blackberry Desktop Manager, connect to the new connection and away you go 🙂
Well as of Friday 7th December I am now RHCT certified (Red Hat Certified Technician)
I managed to pass with 100% which was awesome, now bring on the RHCE!
Over the course of about 2 weeks my raid5 system broke twice requiring new disks and a rebuild.
The controller was a Highpoint RocketRaid 1640 SATA with 4x Seagate 250GB 7200RPM SATAII drives.
Rebuild time was as follows:
Build 1:
raid 5 rebuild started approx 4:25PM
5:27PM – 21%
6:24PM – 40%
7:04PM – 53%
7:28PM – 61%
8:35PM – 82%
9:25PM – 99%
9:27PM – 100%
Build 2:
raid5 rebuild started 11:51AM
2:13PM – 47%
2:51PM – 58%
3:44PM – 76%
4:25PM – 90%
4:55PM – 100%
I couldn’t find any reliable information on an estimated rebuild time, so theres my experience.